It's never too early to reduce the impact of a potential disaster. Having a structured disaster response plan can help your business minimize any destructive downtime and get operations back up and running quickly. These nine tips from IT Pro can help you think through your disaster recovery plan creation and prepare your business for disaster. Read the blog to see what they are and reach out to Abrahams Consulting LLC to build a new disaster...
Managing today's networks requires smarter tools. This solution brief explains how FortiManager, enhanced with FortiAI, helps IT teams automate configuration tasks, detect vulnerabilities with conversational AI, and scale operations without increasing headcount. Download the solution brief to see what GenAI can do for your teams, and contact Abrahams Consulting LLC to discuss how we can help you integrate FortiManager into your workflow.
View:...
Managing multiple document technology suppliers adds cost and complexity, often without improving performance. The solution brief "Your Printing Is So Much More Complicated Than It Needs to Be" breaks down 11 reasons why consolidating vendors is a smart move for efficiency, security, and control. Download the brief to see how consolidation creates a smoother, smarter print environment. Then contact Abrahams Consulting LLC to discuss how your...
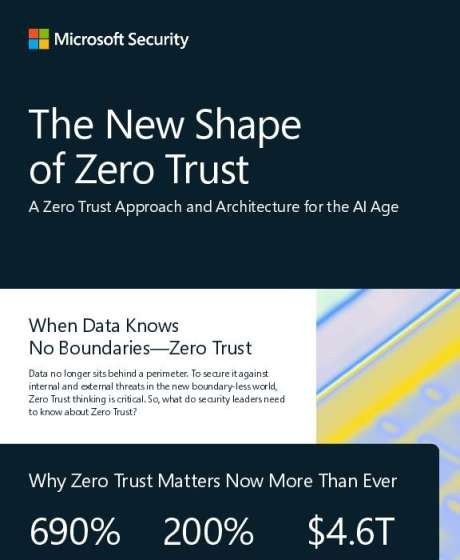
Data flows freely across networks, cloud apps, and AI tools — far beyond traditional perimeters. This infographic shows how organizations can apply core Zero Trust principles to protect assets wherever they live. Check it out to see how to continuously authenticate, enforce least-privileged access, and adapt with AI-powered insights. Contact Abrahams Consulting LLC for guidance on evolving your security model.
View: The New Shape of Zero Trust